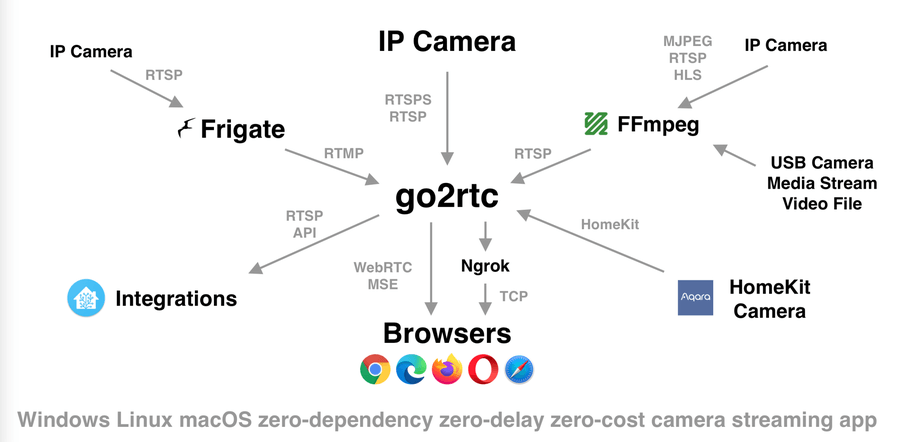
Go2rtc to the public internet can significantly increase security risks. This software acts as a powerful real-time streaming proxy that handles camera feeds, often linked to sensitive locations like homes or businesses. If not configured securely, malicious users can exploit vulnerabilities, intercept video streams, or even gain unauthorized control over connected devices. Internet exposure should always be approached cautiously, with security-first principles guiding every configuration step.
Users often expose Go2rtc to enable remote access to IP camera streams, integrate with third-party applications, or offer browser-based viewing from anywhere. While convenient, this connectivity demands robust protection. Firewalls, encryption, and access controls become mandatory components in safeguarding the underlying services. Neglecting these essentials can lead to compromised privacy and system integrity.
Security risks are not always obvious during initial setup. Misconfigured ports, default credentials, or unprotected protocols can open up pathways for external attacks. Even experienced users can overlook simple mistakes when convenience takes priority over protection. Establishing a framework of best practices reduces these threats while still enabling the functionality users require.
A secure deployment strategy ensures the benefits of Go2rtc are maintained without compromising user safety. Stream availability, performance, and integration should never come at the cost of exposing sensitive environments to potential intruders. Adopting layered security measures creates a resilient structure capable of withstanding targeted and automated cyberattacks.
Using Strong Authentication Methods
Go2rtc currently does not have built-in authentication in the traditional sense. This makes it necessary to implement external authentication mechanisms when exposing streams over the internet. Reverse proxy tools like Nginx, Caddy, or Traefik can enforce HTTP authentication or integrate with OAuth2 systems to provide user-level access control.
Deploying Basic Auth with Nginx is a simple starting point. Administrators can create a password file using htpasswd and configure Nginx to require a username and password before granting access to the Go2rtc stream. Although not the most secure method, Basic Auth still provides a barrier that prevents unauthorized access to unprotected endpoints.
OAuth2 proxy integrations with providers like Google or Auth0 offer significantly stronger protection. These systems authenticate users based on a secure third-party identity provider. Access can then be restricted based on user roles, email domains, or group membership. The added complexity pays off in greater control and auditability.
Strong authentication also reduces the risk of brute-force attacks. If users do not limit access with credentials, automated bots can easily discover and abuse publicly available RTSP or WebRTC streams. Protecting these endpoints with verified authentication methods is the cornerstone of a safe remote streaming environment.
Enforcing HTTPS for Encrypted Connections
All traffic between the client and the Go2rtc server should be encrypted using HTTPS. Encryption prevents eavesdropping and tampering, ensuring that sensitive camera feeds remain private. Without HTTPS, any data sent over the network can be intercepted by malicious actors, especially when traversing untrusted networks like public Wi-Fi or shared ISP infrastructure.
Setting up HTTPS requires an SSL/TLS certificate, which can be obtained freely via Let’s Encrypt. Reverse proxies such as Nginx or Caddy can automatically fetch and renew these certificates. By placing Go2rtc behind a reverse proxy, administrators gain fine control over TLS settings, including cipher suites, HTTP/2 support, and strict transport security headers.
Certificate management should be automated where possible to avoid downtime or expired credentials. Tools like Certbot make the process relatively seamless for most systems. Renewals should be tested periodically to confirm that the certificate infrastructure remains functional under changing network conditions.
A self-signed certificate may suffice in test environments, but it introduces warnings in browsers and potential security holes. For production environments where remote users depend on secure access, trusted certificates issued by recognized Certificate Authorities are necessary. They ensure both encryption and authenticity.
Restricting Access with IP Whitelisting
Another effective method of securing Go2rtc is to implement IP whitelisting. This allows only specific IP addresses or networks to access the exposed service. Firewalls, cloud security groups, or reverse proxy rules can enforce this restriction before traffic reaches Go2rtc.
IP whitelisting is especially valuable for setups where only one or two trusted users need access remotely. For example, restricting access to a home IP address, a mobile carrier IP block, or a corporate VPN reduces exposure to the broader internet. This drastically limits the attack surface.
Firewall tools like UFW, iptables, or built-in router ACLs can implement basic whitelisting. Cloud-based deployments in environments like AWS or Azure benefit from built-in network security policies that support precise inbound and outbound traffic control.
While IP whitelisting increases security, it can also introduce usability challenges. Dynamic IP addresses from ISPs may require frequent updates, and mobile users may encounter access issues if roaming. Dynamic DNS tools or IP-aware VPNs can help manage these situations effectively.
Avoiding Default Ports and Endpoints
Changing default ports for Go2rtc and associated services reduces the likelihood of automated attacks. Most bots and vulnerability scanners look for common ports like 554 (RTSP), 1935 (RTMP), or 80/443 (HTTP/HTTPS). By using non-standard ports, users can avoid being immediately flagged by basic scans.
Go2rtc allows custom port definitions in its configuration file. Administrators should define alternative high-numbered ports that do not conflict with system services. Coupling these with firewalls and NAT rules ensures that only necessary services are reachable from external networks.
Obscurity alone is not a security strategy, but it does act as an initial deterrent. Combined with authentication, encryption, and access control, non-default ports form a useful part of a defense-in-depth approach. They may also reduce log noise and failed access attempts.
Endpoints exposed through HTTP or WebRTC can also be renamed or obfuscated through proxying techniques. Using unique or randomized stream names and avoiding generic URLs like /stream or /camera1 minimizes predictability. These details matter when trying to avoid detection by automated tools.
Keeping Software and Dependencies Updated
Running outdated versions of Go2rtc or its dependencies poses significant security risks. Vulnerabilities may remain unpatched, allowing attackers to exploit known weaknesses. Timely updates are essential to maintain a hardened system.
Go2rtc is actively developed, with regular releases and improvements posted on its GitHub repository. Users should subscribe to update notifications or monitor the release page to track changes. Applying updates periodically ensures access to new features, security patches, and performance fixes.
Reverse proxies, authentication gateways, and operating system packages also need attention. Vulnerabilities in any component of the stack could compromise the entire streaming system. A secure setup involves updating all relevant software layers, not just Go2rtc itself.
Automated update pipelines or containerized deployments can simplify the process. Docker users, for example, can configure scheduled pulls of the latest Go2rtc image, test for stability, and redeploy without manual intervention. Testing updates in a staging environment avoids unexpected downtime or regressions.
Using VPNs for Remote Access
One of the most secure ways to access Go2rtc remotely is through a Virtual Private Network (VPN). VPNs create encrypted tunnels between users and the home or cloud network, shielding the Go2rtc service from direct public exposure.
WireGuard and OpenVPN are two popular solutions for self-hosted VPNs. They offer strong encryption, compatibility across devices, and detailed control over who can access internal services. By routing all access through the VPN, users ensure that camera feeds are never visible to the wider internet.
VPN solutions work well for families, small businesses, or IT professionals who want reliable yet private access to streaming systems. They eliminate the need for complex public firewalls or proxies in many cases. Devices connecting via VPN appear to be part of the local network, allowing seamless integration with Home Assistant and other tools.
Cloud VPN options like Tailscale or ZeroTier provide similar functionality without requiring port forwarding or static IPs. These services abstract the complexity of VPN setup while still providing encrypted, peer-to-peer tunnels. Ideal for users without deep networking expertise, they make secure remote access accessible to everyone.
Minimizing Exposed Features and Protocols
Every additional feature or protocol exposed over the internet increases the potential for exploitation. A security-first Go2rtc deployment should disable all non-essential inputs and outputs, reducing the attack surface as much as possible.
If only RTSP is required, then WebRTC, HLS, or HTTP should be disabled. Unused features become unnecessary liabilities, consuming resources and offering potential entry points. Configuration files should be reviewed and tested for every enabled protocol.
Using go2rtc.yaml, users can tightly control stream availability. Separate internal and external configurations ensure that only designated sources are available remotely. Access to admin or debug endpoints should never be exposed to the public web, as these may leak sensitive system information.
Stream definitions should include access control logic wherever possible. Limiting access to specific device IDs, user agents, or token-based URL parameters enhances security. Streamlining configurations reduces complexity and strengthens the integrity of exposed services.
Monitoring and Logging for Suspicious Activity
A secure system is not just protected—it is observable. Logging and monitoring are essential to detect and respond to threats in real-time. Go2rtc generates logs that reveal connection attempts, errors, and stream performance. These logs should be regularly reviewed to identify anomalies.
Integrating Go2rtc logs into centralized logging platforms such as Loki, Graylog, or Elasticsearch enhances visibility. Users can set up alerts to notify administrators when abnormal behavior occurs, such as repeated failed access attempts or unusual traffic patterns.
Proxies like Nginx can also log request headers, IP addresses, and authentication results. Monitoring tools like Prometheus and Grafana can provide dashboards with live system metrics, helping users stay ahead of performance or security issues.
Persistent logging is crucial for forensic analysis. In the event of a breach, historical logs offer insight into how attackers entered the system and what actions were taken. Without logs, recovery becomes guesswork. Secure configurations include both real-time alerting and historical archiving.
Applying Principle of Least Privilege
The principle of least privilege means granting only the minimum access necessary for each component to function. Go2rtc and its companion tools should not run with administrative or root privileges unless absolutely required. Limiting access reduces the impact of a potential compromise.
System-level permissions should be configured to restrict file access, process control, and network capabilities. Running Go2rtc in a container or a restricted system user account isolates it from the rest of the system. File paths, configuration directories, and log outputs should follow proper permission models.
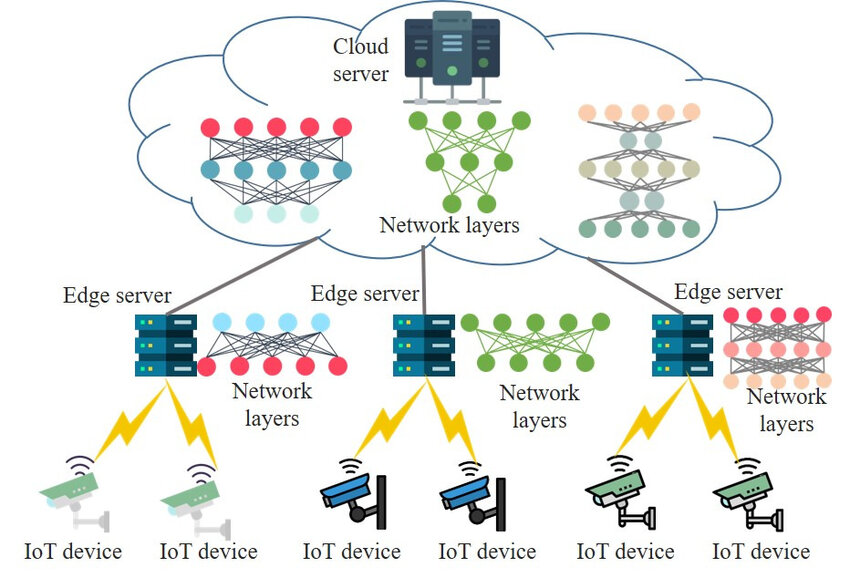
Network segmentation also plays a role in this principle. Internal devices can be placed on different VLANs or subnets, limiting their ability to communicate with each other unless explicitly allowed. Firewalls can enforce these rules, further minimizing the blast radius of an intrusion.
By isolating Go2rtc processes and limiting their scope, users create a more secure system. Even if one component is compromised, attackers cannot easily move laterally or escalate privileges. Granular access control remains a cornerstone of modern cybersecurity.
Conclusion
Securing Go2rtc when exposed to the internet involves a combination of technical safeguards, thoughtful configuration, and proactive monitoring. Authentication, encryption, and network isolation form the foundation of a resilient system. Tools like reverse proxies, VPNs, and firewalls complement these protections and enable safe remote access to live video streams.
Each user’s needs may vary, but the fundamental principles remain consistent. Avoid public exposure unless necessary, minimize available services, and log every critical event. Vigilance, planning, and adherence to best practices ensure that Go2rtc can deliver robust streaming performance without compromising security.